Explore our other capabilities:
Cybersecurity | Enterprise IT Modernization & Optimization | Software Solutions Development & Sustainment

Identity, Credential & Access Management
- Personal Identity Verification; HSPD-12; Zero Trust
- Modern ICAM Solutions; FIDO; Federation; Single Sign On
- Enterprise Logical and Physical Access Control
- Public Key Infrastructure; Encryption and Digital Signature
There is a pressing need to secure federal physical and digital infrastructures and standardize secure access to them. Various government policies, including Homeland Security Presidential Directive (HSPD-12) and Office of Management and Budget (OMB) Memorandum M-19-17, drove the development of identity standards by the National Institute of Standards and Technology (NIST), notably the Federal Information Processing Standard (FIPS) 201 and Special Publication (SP) 800-63.
These initiatives ushered in the age of Personal Identity Verification (PIV) cards and Common Access Cards (CACs), which offer strong authentication options. More recently, FIDO Alliance passkey initiatives and the federal zero trust architecture (ZTA) initiative are further transforming federal authentication and authorization requirements.
Federal agencies face complex compliance challenges in this dynamic environment. Understanding the regulatory requirements is one hurdle, while security and privacy architecture development, implementation, and operation is another. Organizational change management is perhaps the greatest challenge of all when strengthening ICAM implementations.
Electrosoft possesses over 15 years’ experience in this highly specialized field – and a solid record of accomplishment. We are a respected HSPD/ICAM thought leader whose contributions include co-authorship of key NIST PIV publications; solution development and implementation in multiple federal agencies; and initiation and operation of the FIPS 201 Evaluation Program.
Areas of Specialization

- Personal Identity Verification; HSPD-12; Zero Trust Read More >
- Enterprise Logical and Physical Access Control Read More >
- Public Key Infrastructure; Encryption and Digital Signature Read More >
- Modern ICAM Solutions; FIDO; Federation; Single Sign On Read More >
Client Stories
DevSecOps Team Modernizes Complex Logistics Applications, Enhancing Security and Efficiency
PACS Lab Establishes Evaluation Requirements and Approves First Facial Authentication Reader for Federal Use
-
- Electrosoft researched and documented the facial reader authentication requirements and identified a matching algorithm success requirement based on National Institute of Standards and Technology (NI... Read More >
Implementing Multifactor Authentication in a Standalone Operating Environment
-

- A small independent federal agency chartered with responsibility for select commerce activities sought to comply with Executive Order (EO) 14028, which requires agencies to implement specific actions... Read More >
Creating Efficient, Compliant, Secure ID Credentialing and Visitor Access
-

- For one government agency’s ID Card Office, Electrosoft implemented process and technology improvements to support government information processing Read More >
Improving Enterprise Security through User Access Governance
-
- Electrosoft provides Identity, Credential and Access Management (ICAM) expertise to enhance the cybersecurity posture of a civilian agency that oversees many U.S. financial institutions. Read More >
Establishing a Comprehensive FIPS 201 Evaluation Program
-

- Electrosoft designed and initiated a comprehensive conformance testing program for the evaluation of supplier products and services against applicable Federal standards and guidelines. Read More >
Implementing an Enterprise Physical Access Control System
-

- Electrosoft designed and implemented the ePACS solution to present a common workflow for access provisioning/de-provisioning for all of the Department’s physical facilities regardless of the specif... Read More >
Implementing a PIV-Enabled Visitor Management System
-

- Electrosoft designed, configured and implemented an enterprise-level visitor management system that interfaces with a variety of facility access control solutions. Read More >
Providing Operational Support for HSPD-12 Program Management Office
-

- Electrosoft experts analyzed emerging policies, standards and trends related to Federal identity, credential and access management to support a Civilian Department’s desire to remain at the leading... Read More >
Strengthening Security Posture through PIV Card Issuance, Authentication and Single Sign-On
-

- Electrosoft assisted an independent oversight agency in obtaining Personal Identification Verification (PIV) cards for all agency personnel. Electrosoft also designed, configured and implemented an e... Read More >
Providing Security Analyst Services for Emerging Health Technology
-

- Electrosoft performed in-depth research to identify, analyze and validate emerging technologies, healthcare trends, policies, standards and guidelines. Read More >
Developing Cybersecurity, Identity Management, and Encryption Standards and Guidelines
-
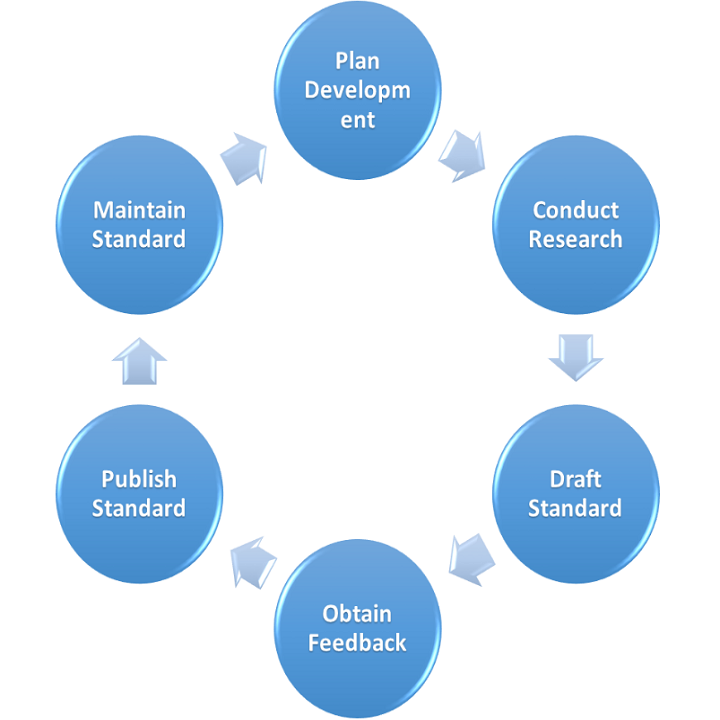
- Electrosoft’s team of world-class experts worked closely with Government researchers to define, develop and refine needed technical standards and guidelines. Read More >
Beating the Clock on a Ticking Black Box: Electrosoft Saves an Essential FIPS Testing Tool
-

- Physical access control is a fundamental government security requirement, assuring that only authorized individuals (employees and contractors) can enter government systems and facilities. The federa... Read More >